Ransomware is becoming one of the more common types of malware and its prevalence is growing fast. With sanctions taking their toll on the Iranian economy, Iranian hackers have ramped up their development and deployment of ransomware to make a quick dollar online. 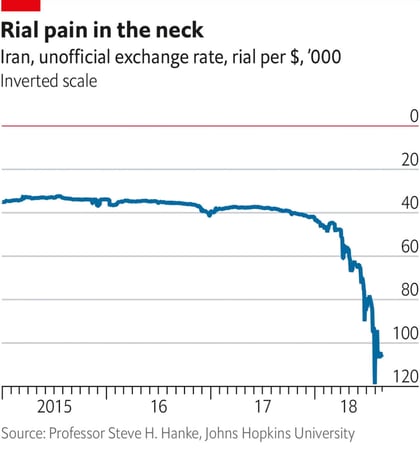
Rather than targeting one high-value organization for a single large payout, ransomware attacks often cast a wide net targeting many lower profile businesses for smaller amounts of money which adds up to a huge payday in the end.
The attacks are taking a toll on all types of organizations and regardless of location. Whether you are a Vermont, a New York, a New Hampshire, or a Colorado-based business, you are just another IP address on an attackers map. Why should you pay attention to ransomware? A ransomware attack can inflict severe damage to your business by encrypting all of your digital files, making the data inaccessible to you.
A recent ransomware attack on a Colchester, Vermont based company has been described by the owner as the worst thing that's ever happened to the business.
The company lost seven months worth of records in the attack, despite having a system in place to backup data. Even worse, Vermonters personally identifiable information may have been accessed by hackers in the attack which they can exploit to steal your identity. While this is less than ideal, the company should be applauded for their transparency, alerting the media and customers about the breach, a rare action for a company that has suffered a cyber incident. While their are laws mandating when and how a company reports a data breach, words such as "breach," "incident," and "vulnerability" can be subject to interpretation. Many companies choose to wait years before reporting and incident if they report it at all.
This attack has business owners in Vermont, New Hampshire, New York, Colorado, and across the United States asking themselves, how can I prevent my business from being breached?
6 Ransomware Prevention Tips:
1.) Utilize a EndPoint Protection software specifically designed to prevent ransomware attacks
Software like Intercept X is specially designed to prevent ransomware attacks. By leveraging deep learning neural networks and behavioral analysis Intercept X can detect and prevent never-before-seen strains of ransomware.
2.) Avoid paying the ransom at all costs
After getting hit by ransomware Wendell's Furniture in Vermont paid an undisclosed ransom to regain access to their data, a risk you should never take if you're the victim of ransomware. The keys to unlock files encrypted by certain strains of ransomware are available for free on sites like nomoreransom.org. Of the people who pay the demanded ransom, not even 20% regain access to their data. Paying the ransom is a risky toss of the dice with the only guaranteed outcome being the enrichment of the hacker who did this to you.
3.) Perform a Risk Assessment
Be proactive! A Risk Assessment is an affordable and reasonable way you can help protect your business. Risk assessments identify and remediate weaknesses in your IT security and privacy. You'll greatly reduce your risks by following a plan based on a risk assessment, saving you time and money over the long haul.
4.) Verify IT resources have the skills to tackle today's IT Security Aspects
The IT world changes rapidly making it crucial that the IT resources working for you undergo frequent training to understand the importance of new processes, services, and tools that serve as key elements in a strong Security Operations Plan. If regular changes aren't being made in your computing and employee education environment, your defenses are likely falling behind.
5.) Implement Next-Gen endpoint protection and MSSP
By keeping your devices updated with security patching, next-generation end point protection and managed services will help guard against all sorts of malware components, including ransomware.
6.) Utilize a spam filter in the cloud
An effective spam filter can keep malware from ever reaching your premise. Unfortunately, not all filters are the same and some of the most popular ones aren't the most effective. Utilizing Multi-Threat Protection (MTP) is a great way to ensure your systems are secure in the cloud with email and spam protection.
No matter where your business is located, be it New York, Vermont, New Hampshire, Colorado, or anywhere else, we're all neighbors online and everyone is a target today. A proactive approach to security is the best way to make sure you're not the next ransomware victim making headlines. Too many businesses are sitting on the sidelines thinking a cyberattack won't happen to them - with a new ransomware attack being launched every 14 seconds the time to act is now.
Getting hit with ransomware can be scary. If you find yourself the victim of a ransomware attack don't panic, reach out to a cybersecurity expert who can guide you on your path to recovery. Investing in cybersecurity doesn't have to be an expensive grand undertaking if you find service provider who can deliver solutions tailored specifically to your business's size and needs.
Read More:

COMMENTS