Whether you realize it or not, phishing scams are virtually in every inbox at one point or another. In fact, some inboxes get dozens a day, but we don’t realize it because of our junk and spam folders. However, just because our email accounts have the safety net of a spam folder, that doesn’t make our email accounts impenetrable. Hackers are masters at getting phishing emails and other scams through and straight to your inbox without being detected.
What is phishing?
Phishing is a term used to identify the act of attempting to obtain data and personal information from someone. Most often, for a malicious reason, hackers will disguise emails, phone calls, websites, instant messages and more to trick people into falling for whatever plan they have going on. Once the person who is being deceived has fallen for the attack, hackers are able to obtain what they were after; passwords, credit card information, direct access to your bank account, and even demands for money.
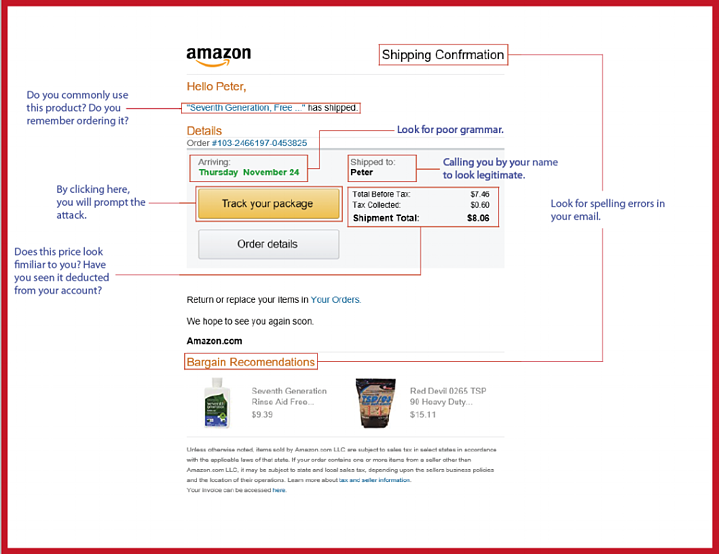
You may be wondering how people fall for these tricks every day and that this would never happen to you, but the truth is it can very easily. Hackers spend a lot of time crafting clever messages that appear so real that you wouldn’t think twice while looking at them.
Phishing is a pretty broad term. When we take a deeper dive into the act of phishing, we begin to see that there are different types or techniques of phishing that are commonly used. Without knowing the different techniques used to trick users, it is difficult to identify something that is real and something that is malicious.
Spear Phishing
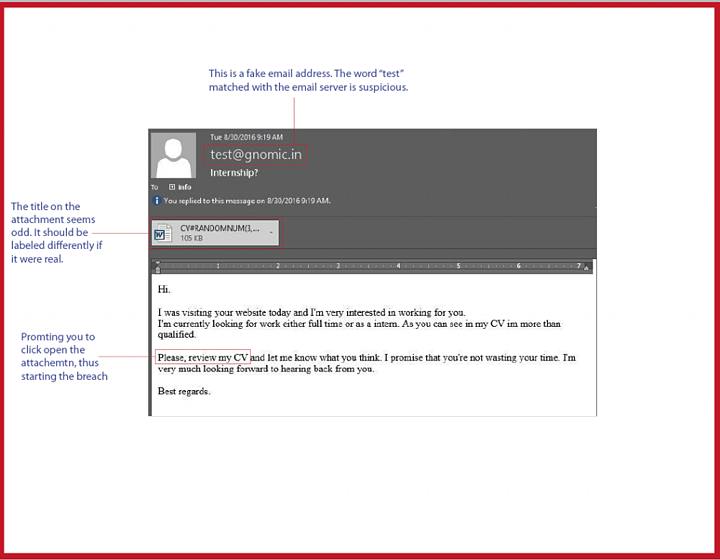
Spear phishing is a term that’s often used for fraudulent emails or other direct messages that target a specific company or certain people within a company in an attempt to access their confidential information. Ultimately, the hacker’s goal is to send a legitimate looking email to a group within a company in hopes that one or more employees will look at it and think it’s real. An example of this could be an email that looks like a company memo to a specific department with perhaps an attachment included that holds a virus. If it is an important company memo, then the chances that employees will read it and click open the attachment is high. That’s exactly what hackers are hoping for. These tactics have long been common through emails, but as technology advances and people are more accessible through social media, attacks have also been conducted through Facebook, Twitter and LinkedIn.
This tactic is also used for phone calls. Perhaps you have received calls before by someone who specifically calls you by your name and says that they are from a bank and a loan payment is overdue. Or perhaps they pretend to be a family member who has been involved in an emergency situation and needs money right away. All of these examples happen often and tend to be very effective.
Whaling
To keep with our “phishy” theme, another typical technique is Whaling. This is a type of fraud that specifically targets high-profiled corporate users. Politicians, celebrities, corporate executives and the like would all fall into this category if they were to be attacked. The term “whaling” is given to these more spotlighted targets because they are the big-fish and pose an extra challenge for hackers to successfully exploit.
The end goal of whaling is to trick someone into disclosing either personal or corporate information. Emails, phone calls or other forms of direct messages can be sent and seem perfectly legitimate in nature. These messages can be even trickier for the victims to identify because hackers tend to know an incredible amount of information about high-profile targets. With targets like this, it is easy to conduct a quick web search of a celebrity, politician or corporate executive and find out vast amounts of information about them to use to their advantage.
Pharming
This technique is especially malicious because there isn’t a true way to identify that you’re being phished. Pharming is essentially when a hacker creates a website identical to another in order to trick you when you log on by simply changing the website’s address ever so slightly. Imagine you go to your banking website to check your accounts. You go to log in and everything looks the same, but in reality, the website you’re on was corrupted and instead of your information going to the banking website, it is funneled further to this mock website which is completely controlled by a hacker. This is done so well and so carefully that the majority of people don’t realize it has even happened or that they just gave all of their important information straight to a hacker.
As a technique, pharming has proved effective because rather than “baiting” the victims, they naturally come straight to the hackers. In order to protect against attacks like this, businesses should encourage employees to only log in to HTTPS-protected sites.
Dropbox Phishing
In the past few years, Dropbox has become popular for backing up and accessing files. So naturally, this is tempting for hackers as millions of people and businesses rely heavily on Dropbox for storage. In some examples, attackers attempt to lure users into entering their login credentials to access a fake, but identical Dropbox sign-in. Once the user enters their credentials, they have access to all of your files without you even being aware of the attack.
Companies should seriously consider investing in User Awareness training for their employees.![]()
To help ensure security of not only your personal data, but also the data of your company, the first wave of defense is your employees. Companies should seriously consider investing in User Awareness training for their employees so they understand how to recognize all of these attacks and can, therefore, avoid them. Educating yourself and your employees on how to properly report an attack is also critical to maintaining your network’s integrity. Employees are just the first step to what needs to be an overall cybersecurity investment on behalf of the company.
Read More:

