You only need to tune into the news for a short time to understand that hostile governments are doing everything they can to steal valuable information anywhere they can get it. Of particular risk to our national security are sensitive defense related secrets. However, the Department of Defense has identified that it’s not just information marked by some form of ‘classification’ that can be valuable to a hostile foreign power. There are large amounts of information throughout the defense acquisition system that could be valuable to foreigners if compromised.
In response to this widely dispersed and highly valuable information being at risk, the Defense Department has amended the Defense Federal Acquisition Supplement (DFARS) to impose cybersecurity safeguards across the defense acquisition system.
In the world of compliance, the drafted documentation often leads to more questions than it does solutions. NIST Special Publications can be lengthy, and the revision process adds and removes information which can provide even more frustration when trying to make sure internal policies and procedures are mapped exactly to the publications. To assist you in your quest to be better secured, we have drafted a quick reference for some of the more popular questions we’ve come across when following a NIST recommendation.
What is DFARS?
The Defense Federal Acquisition Regulation Supplement or DFARS, supplements the Federal Acquisition Record (FAR) which governs how the federal government acquires supplies, materials, and services. The supplement - DFARS - is an addendum of rules, regulations codes and guidelines that the Department of Defense maintains in order to manage their acquisition processes as an arm of the US Government.
Clearly the DoD has specific needs and management prerogatives that the rest of the government does not. The DoD system, in order to function handles a wide range of valuable, sensitive, and classified information. The system that comprises the DoD acquisition network is vast and it’s easy to see how all manner of information held within this system could be valuable to our adversaries around the world. The DFARS supplements the FAR framework in order to stretch it to cover the DoDs acquisition management needs.
Why is DFARS important to manufacturers?
Manufacturers within the defense procurement system hold a special place in terms of possible security risks for a variety of reasons. The most obvious is that the DoD manufacturing system can hold all kinds of information that if stolen, would reduce the edge that we hold in defense technologies or allow adversaries to understand our designs and how to defend against or to harm us.
Our enemies are after information as arcane as scientific research and testing results and sophisticated software modeling capabilities that enable simulations of complex systems such as radar evading surfaces or noise inducing marine profiles to more obviously valuable information such as engineering drawings of upcoming hardware roll outs. However, even seemingly mundane information such as ERP (Enterprise Resource Planning) reports could be valuable to an enemy power wanting to see where key supply chain points are, what types of spare parts are available in the system or the progress of fulfilling ongoing production contracts.
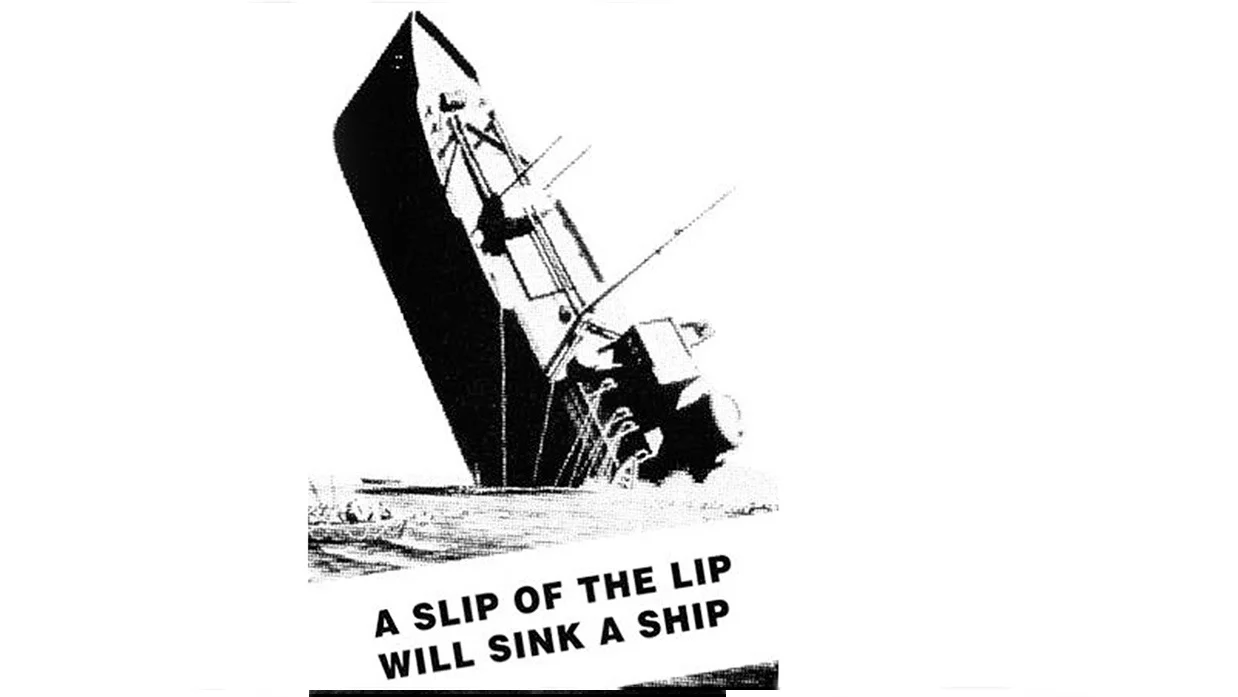
So in a way ‘loose lips sink ships’ is still relevant, it’s just that in addition to leaks from people, poorly protected information technology systems throughout the defense acquisition system are equally and perhaps vastly more risky than what a single person might purposely or inadvertently expose.
NIST Special Publication 800-171
So what is the Department of Defense to do when faced with a challenge as large as protecting an entire manufacturing ecosystem from prying eyes? One step that they’ve taken is mandating that all DoD contractors that store, process or transmit Controlled Unclassified Information (CUI) must meet the requirements of NIST Special Publication 800-171 “Protecting Controlled Unclassified Information in Non-Federal Information Systems and Organizations.” by December 31, 2017 or risk losing their contracts.
These controls must be in place at both the contractor and subcontractor level, ensuring that the entire procurement chain is at least minimally protected from creeps, cheats and thieves.
Following 800-171 guidance is extremely important to maintaining existing DoD contracts, as the deadline for implementing changes has already passed. There is no time like the present to update or create policy and procedure documentation. Even showing that you've taken steps towards following 800-171 can put you ahead of your competitors.
We believe that every organization has their own level of CUI as well. You may not have CUI directly in a contract, however any piece of information that differentiates you from your competition can be treated and secured just like CUI. NIST SP 800-171 is a tremendous recommendation to follow to protect your important information, assets, and trade secrets.
What's CUI and Do I Need to Worry About it?
This leads to a question for DoD contractors and manufacturers, what is Controlled Unclassified Information or CUI?
The information classification of CUI was created by Executive Order 13556. Executive Order 13556 applies broadly across all branches of government, however it provides definitions of CUI for the DoD as well.
This order defines the types of information government wide which should be kept confidential. The goal of this executive order was to standardize and apply consistent protections to sensitive information held by the government and related entities such as regulated industries and government contractors. Sensitive information is information that falls below the well-known secrecy classifications used by certain law enforcement and defense agencies but is still information that should be protected.
As a result the types of information covered by this executive order can be quite broad and can include things from Personally Identifiable Information (PII), to production information about certain types of industrial chemicals that might be used to create havoc, to documents related to government budgeting.
For manufacturers working with the DoD, CUI can include anything marked ‘for official use only’, ‘confidential’ or other similar markings.
The Defense Federal Acquisition Regulation Supplement (DFARS) clause 252.204-7012 (Revised Oct 21, 2016), Safeguarding Covered Defense Information and Cyber Incident Reporting includes a definition for manufacturers that in part says “unclassified controlled technical information or other information, as described in the Controlled Unclassified Information (CUI) Registry, that requires safeguarding or dissemination controls pursuant to and consistent with law, regulations, and Government-wide policies, and is:
- Marked or otherwise identified in the contract, task order, or delivery order and provided to the contractor by or on behalf of DoD in support of the performance of the contract; or
- Collected, developed, received, transmitted, used, or stored by or on behalf of the contractor in support of the performance of the contract.
Generally it’s safe to assume that for DoD contractors, all contractual documents from the government as well as things like purchase orders and sub-component specifications, engineering data and drawings, technical reports, bills of materials, source or executable computer code, specifications, any written or electronic communications about any of the above would fall under the CUI umbrella. However, “in support of the performance of the contract” is quite broad, so organizations who are audited for compliance need to keep in mind that they have a broad responsibility to maintain the security of a very wide range of information.
Any subcontractor to the DoD would be subject to the requirements to protect this information but manufacturers in particular, because of the amount of CUI they are likely to possess are at particular risk of non-compliance.
Remember, at this point in time, failure to follow guidelines can lead to cancellation of valuable government contracts.
Does NIST SP 800-171 require encryption at rest?
This requirement is in the scope of 3.13.16 Protect the confidentiality of CUI at rest which references control SC-8 within another NIST Special Publication, SP 800-53, “Security and Privacy Controls for Federal Information Systems and Organizations”.
CUI can be stored at rest in any non-mobile devices or data center unencrypted, as long as it is protected by other approved logical or physical methods. This can be accomplished using cryptographic mechanisms and file share scanning. The stress here is documenting how information is stored and then adequately protected, and confirming that methods used for protection are approved.
What Does DFARS Compliance Look Like?
Per DFARS, defense contractors must be able to demonstrate ‘adequate security’ as well as complying with cyber incident reporting. Per DFARS, ‘adequate security’ means ‘protective measures that are commensurate with the consequences and probability of loss, misuse, or unauthorized access to, or modification of information’.
In practice, DFARS has mandated that contractors and sub-contractors throughout their systems follow the guidance within NIST Special Publication 800-171 “Protecting Controlled Unclassified Information in Non-Federal Information Systems and Organizations.”
NIST Special Publication 800-171 defines the NIST Cybersecurity Framework.
Is Office 365 Compliant With 800-171?
FedRAMP-certified products offer more streamlined compliance but is limited to government entities. Office 365 can be configured and managed to address controls set forth by 800-171. Again, focusing on proper documentation is key, especially when proving that the controls in place are adequate as an “alternate control”. There is no cookie-cutter approach, but compliance can be achieved in different ways.
What Are Basic and Derived Controls?
“The basic security requirements are obtained from FIPS Publication 200, which provides the high-level and fundamental security requirements for federal information and systems. The derived security requirements, which supplement the basic security requirements, are taken from the security controls in NIST Special Publication 800-53.” (NIST SP 800-171. Page 6).
The important thing to note about both basic and derived security requirements can be mapped to controls listed in 800-53, which we have found provides a great insight into each control. These mappings can be found in Appendix D (Tables D-1 through D-14) within the NIST SP 800-171 document.
Fortunately, NIST has provided a Self-Assessment Handbook that offers an in-depth guide that coincides with their recommendations from 800-171, and can assist with any compliance efforts.
What's The NIST Cybersecurity Framework?
The NIST Framework for cybersecurity is a tool to be used by small and large organizations – and all sizes in between – to enhance their ability to prevent, defend, and respond to cybersecurity risks. In short, it’s a guide to ‘help identify, assess, and manage cyber risks in a cost-effective way to address cybersecurity risks which pose threats to our nation’s security, economy, public safety, and health’.
If you think about it, nearly every organization serves the public in some form or other and could be affected by a cyber threat. What organization doesn’t obtain credit card information, home phone numbers and addresses, cell phone numbers, and other personally identifiable information in some fashion?
Meeting the needs of such a broad range of organizations requires a standard that is flexible yet powerful. NIST accomplishes this by taking a ‘risk-based’ approach. It falls on individual organizations to identify and manage their own risk profile and provides a guided framework to help people within those organizations to get to the right result. Because of the wide-ranging multitude of possible vulnerabilities, using a risk-based approach assists with weighing the likelihood something would affect your organization, enabling prioritized and cost-effective action.
With the evolution and adaptation of cyber threats, the NIST Framework has to change, too, undergoing reviews and updates as new events occur, cutting-edge breakthroughs deliver new knowledge, and others share their lessons learned.
For most companies, implementing the NIST Cybersecurity framework is optional. It’s a helpful rubric for CISOs and other IT professionals to assist with analyzing their risks and securing their IT infrastructure.
The difference today is that for Defense Contractors, this is now mandatory and the potential loss of valuable contracts for non-compliance is a significant ‘stick’ to ensure compliance.
Focusing on these changes today may open up opportunities for your organization in the future as well. Plus, it's just a good practice to keep your business, in business.
The meat of the NIST Cybersecurity Framework consists of three elements:
These components of the Framework help guide you through ‘a risk-based approach to managing cybersecurity risks’. The processes provide considerations to help you through a review to accurately describe your current cybersecurity posture, then to consider your goals, where you need and/or want to be.
With these items defined you can accurately detail what can be done to bridge the gaps. This third stage is intended to be ongoing, “a continuous and repeatable process” (p.4). The next steps, assessing and communicating, are also constant processes – you’re assessing your current state compared to your goals, and you’re communicating that information to ‘internal and external stakeholders’.
Additional Resources
- NIST SP 800-171
- NIST Special Publication SP 800-171 “Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations” provides requirements for protecting the confidentiality of Controlled Unclassified Information (CUI).
- Helpful information for manufacturers related to NIST
- DFARS Cybersecurity Guidelines
- http://www.acq.osd.mil/dpap/dars/dfars/html/current/204_73.htm
- More on CUI



